Iran’s Malign Intelligence Activities
Download ReportMalign International Activities
Page Navigation
The Ministry of Intelligence (MOI) and Islamic Revolutionary Guard Corps Intelligence Organization (IRGC-IO), play a crucial, constitutionally-mandated supporting role in Iran’s efforts to preserve and export the Islamic Revolution. While the Quds Force—the IRGC’s foreign expeditionary force—is at the forefront of Iran’s global campaign of state-sponsored terrorism and subversion, Iran’s intelligence agencies play an active role behind the scenes, providing material, technical, logistical and operational support to the Quds Force and Iran’s terrorist proxies, including Hezbollah, Hamas, and various Shi’a militias. At times, the MOI and IRGC-IO act independently of one another to further Iranian foreign policy objectives.
Preserving the Revolution
Even in the international arena, the primary focus of Iran’s intelligence agencies is the domestic imperative of preserving the revolutionary regime. Political and ethnic dissident groups of various stripes are active abroad, and the MOI plays the leading role in monitoring, infiltrating, and sabotaging these groups on foreign soil.
Following the Islamic Revolution, Ayatollah Khomeini’s newly installed Revolutionary Council immediately set about trying to eliminate potential nodes of opposition and as part of that effort, Iranian intelligence agents abroad undertook a campaign of targeted assassinations against exiled dissidents. According to the Iran Human Rights Documentation Center, Iranian intelligence agents have been linked to the assassination of at least “162 monarchist, nationalist, and democratic expatriate activists” in 19 different countries. A detailed accounting of the known victims of Iran’s international assassination campaign and its perpetrators can be found here.
The earliest targets of the assassination campaign were monarchists critical of the revolutionary regime. In December 1979, Prince Shahriar Shafiq, a 34-year-old nephew of the Shah, was shot to death in Paris, France, the first victim of extrajudicial assassination abroad. Shafiq was forced into exile due to his efforts to organize resistance to Khomeini’s revolutionary government, activities which he continued upon his arrival in France. On his way to visit his also-exiled mother’s apartment, a gunman concealing his identity with a motorcycle helmet shot him twice, killing him. Ayatollah Sadegh Khalkhali, a prominent regime official who served as the first religious magistrate of Iran’s revolutionary courts, published a statement in the hardline newspaper Kayhan claiming that members of the faction he led, fadaiyan-i Islam (Devotees of Islam), were behind the killing. Khalkhali further vowed that his guerilla fighters would continue to target former regime figures.
In July 1980, Khomeini’s agents struck in Bethesda, Maryland, a suburb of Washington, DC. Ali Akbar Tabatabai, a diplomat who served as the country’s press attaché in Iran’s US embassy under the Shah was shot and killed in his home by Daoud Salahuddin, an African-American Baptist convert to Islam sympathetic to Khomeini’s Islamic Revolution. Tabatabai became a prominent critic of Khomeini following the Islamic Revolution and founded the Iran Freedom Foundation, an organization that advocated for replacing Khomeini’s regime with a secular democracy. According to his assassin’s account, Salahuddin accepted several thousand dollars from a representative of Khomeini’s government to carry out the plot, which involved disguising himself as a postal worker. After executing the assassination, Salahuddin’s accomplices helped him escape to Iran via Canada and Switzerland. He has lived in Iran as a fugitive shielded from justice by the Iranian regime to present day. In 2007, Salahuddin was the last known person to have had contact with Robert Levinson, a former FBI agent who remains missing in Iran.
Revolutionary paramilitary organizations such as fadaiyan-i Islam formed the basis of Iran’s early intelligence community, and they pursued regime opponents abroad on an ad hoc basis. Upon the creation of the MOI, the assassination campaign became a “coordinated government action in which Iranian intelligence officers and soldiers of the Revolutionary Guards’ elite Quds Force provided the tip of a spear wielded against the opposition by the Special Affairs Committee, an extraparliamentary body comprised of some of the most powerful executive political figures in the country.”
The MOI-led assassination campaign would continue until 1999. The international campaign increased in scope and intensity during the period concurrent with the “chain murders” in Iran, from 1988-1998. The increasing reliance on assassinations was largely the handiwork of President Rafsanjani’s intelligence minister Ali Fallahian, who was also the chief architect of the domestic assassination campaign against regime opponents. After the MOI was purged of many of its most hardline staffers in the wake of the discovery of the chain murders, the international assassinations tapered off as well.
One of the more sensational assassinations during this period took place in Switzerland in April 1990 and targeted Kazem Rajavi, the brother of MEK leader Massoud Rajavi. Two cars ran Rajavi’s vehicle off the road, after which armed gunmen exited one of the cars and executed Rajavi. Swiss investigators issued a report naming 13 suspects believed to be Iranian intelligence officers. According to the report, “all 13 came to Switzerland on brand-new government service passports, many issued in Tehran on the same date. Most listed the same personal address, Karim-Khan 40, which turns out to be an intelligence ministry building.”
In August 1991, Iranian operatives stabbed to death one of the most prominent exiled opposition figures, Dr. Shapour Bakhtiar, and his secretary in his Paris apartment. Bakhtiar was a political opponent of the Shah who the Shah appointed as his final prime minister in a last-ditch effort to prop up his crumbling government at the end of 1978. During his short-lived tenure, Bakhtiar sought to rapidly implement political reforms in an effort to pacify Khomeini’s revolutionary forces. Khomeini, insisting on nothing less than the overthrow of the monarchy, rejected Bakhtiar’s government and denounced him for collaborating with the Shah. Bakhtiar fled Iran shortly after the Islamic Revolution in April 1979.
Bakhtiar was one of the former regime figures marked for assassination by Ayatollah Khalkhali, the first magistrate of Iran’s revolutionary courts immediately following the revolution. Upon his emergence in Paris, Bakhtiar founded and led the National Movement of the Iranian Resistance. This organization connected Bakhtiar to Ali Akbar Tabatabai, who served as Bakhtiar’s primary spokesman in the US In July 1980, Khomeini thwarted a coup plot led by Iranian military officers at the Nojeh air base which Bakhtiar was accused of backing. Shortly thereafter, Bakhtiar survived the first assassination attempt on his life by Khomeini’s agents. One of the would-be assassins later implicated the Iranian regime in the plot, stating in a 1991 interview, “I had no personal feelings against Bakhtiar … It was purely political. He had been sentenced to death by the Iranian Revolutionary Tribunal. They sent five of us to execute him.” In 1991, three Iranian operatives were dispatched for another assassination attempt on Bakhtiar, this one successful. Two of the assassins escaped to Iran while the third was apprehended in Switzerland and extradited to France. The assassin received a life sentence, but was paroled in 2010 and subsequently repatriated to Iran.
Perhaps the most “daring and public“ incident during this time period was the elaborately planned assassination of four Kurdish democracy activists at the Mykonos Restaurant in Berlin, Germany on September 17, 1992. The Mykonos plot was carried out by a Hezbollah cell acting under the orders of the Iranian government and with direct participation by MOI operatives. An Iranian defector with ties to the security establishment alleged that the decision to carry out the attack was made by Iran’s Special Affairs Committee, which included President Rafsanjani, Intelligence Minister Fallahian, former Foreign Minister Ali Akbar Velayati, and Supreme Leader Khamenei himself. In the run up to the attack, Fallahian gave a series of interviews in which he boasted that Iran surveilled dissidents abroad and had already eliminated some top regime opponents.
An MOI operative trained in Lebanon led the “attack group” behind the Mykonos assassination and served as one of the two gunmen. The other gunman, and many of the co-conspirators in the attack were Hezbollah members based in Germany. The MOI was instrumental in the logistics of the attack, conducting surveillance of the targets and securing the weapons and silencers used. Following Germany’s investigation into the attack, the federal prosecutor issued an arrest warrant for Ali Fallahian for ordering the attack. Khamenei, Rafsanjani, and Velayati would also be charged for their roles in the plot in November 1996.
The revelation of the MOI’s role in the chain murders, along with rising international condemnation and pressure from countries where Iranian intelligence operatives had carried out assassinations, led the Islamic Republic to abandon the practice by 1999. Since that time, Iran’s external intelligence apparatus has shifted its focus to harassment, intimidation, and delegitimization of dissidents abroad.
Embedded Iranian intelligence agents “have been known to monitor dissidents by infiltrating and observing their meetings and speeches, and MOI officers often want dissidents to know they are being watched so that they will be intimidated.” Iranian intelligence frequently engages in disinformation campaigns to tarnish the reputation of dissident groups abroad and to sour their relations with host countries, a tactic it learned from the Soviet KGB. In 2013, for instance, at the Obama administration’s urging, Albania offered asylum to up to 2000 Iranian MEK dissidents. In response to their presence, Iranian media outlets began publishing articles in Albanian meant to discredit the MEK. In May 2017, the Islamic Republic of Iran Broadcasting (IRIB) announced the launch of a 24-hour Balkan Network featuring Bosnian and Albanian language programming meant both to propagate the Iranian regime’s religious and geopolitical worldview, and to influence public opinion against the MEK.
Iran has also launched complex operations in recent years to lure dissidents into third countries, which offer Iranian intelligence a permissive environment, and to kidnap them while there. Recent cases include the late dissident journalist Ruhollah Zam, the son of a former regime official, who ran a popular Telegram channel called Amad News. Beginning in 2011, Zam had lived in exile in France under police protection. In 2019, he was lured to Iraq with false promises of funding for a media project, and abducted there by the IRGC. Zam was later executed in December 2020 for the crime of “corruption on earth.”
The regime also kidnapped Jamshid Sharmahd, a California-based operative of the Kingdom Assembly of Iran’s Tondar opposition group, in Dubai. After, based on cell phone data, Iranian operatives took him to Oman and then to Iran. The regime accused Sharmahd, a German citizen, of complicity in a 2008 attack on a mosque, but Sharmahd’s family denies the allegation, saying he was merely a spokesman for the group. A similar modus operandi was employed in Iran’s abduction of Habib Chaab in Turkey. Chaab, a founder of the Arab Struggle Movement for the Liberation of Ahvaz (ASMLA) and a Swedish citizen, was lured to Istanbul using an MOI “honey trap.” This entailed the use of a female Iranian spy who enticed Chaab to travel to Turkey under the pretext of a romantic meeting. He was then kidnapped and smuggled across the border into Iran. There, he appeared on state television, with an alleged coerced confession to engaging in terrorism. Thus, the IRGC and MOI have both been using this tactic.
 Authorities thwarted an Iranian terrorist attack targeting the July 2018 Paris convention of the National Council of Resistance in Iran.
Authorities thwarted an Iranian terrorist attack targeting the July 2018 Paris convention of the National Council of Resistance in Iran.
In July 1980, Khomeini’s agents struck in Bethesda, Maryland, a suburb of Washington, DC. Ali Akbar Tabatabai, a diplomat who served as the country’s press attaché in Iran’s U.S. embassy under the Shah was shot and killed in his home by Daoud Salahuddin, an African-American Baptist convert to Islam sympathetic to Khomeini’s Islamic Revolution. Tabatabai became a prominent critic of Khomeini following the Islamic Revolution and founded the Iran Freedom Foundation, an organization that advocated for replacing Khomeini’s regime with a secular democracy. According to his assassin’s account, Salahuddin accepted several thousand dollars from a representative of Khomeini’s government to carry out the plot, which involved disguising himself as a postal worker. After executing the assassination, Salahuddin’s accomplices helped him escape to Iran via Canada and Switzerland. He has lived in Iran as a fugitive shielded from justice by the Iranian regime to present day. 2007, Salahuddin was the last known person to have had contact with Robert Levinson, a former FBI agent who remains missing in Iran.
Revolutionary paramilitary organizations such as fadaiyan-i Islam formed the basis of Iran’s early intelligence community, and they pursued regime opponents abroad on an ad hoc basis. Upon the creation of the MOI, the assassination campaign became a “coordinated government action in which Iranian intelligence officers and soldiers of the Revolutionary Guards’ elite Quds Force provided the tip of a spear wielded against the opposition by the Special Affairs Committee, an extraparliamentary body comprised of some of the most powerful executive political figures in the country.”
The MOI-led assassination campaign would continue until 1999. The international campaign increased in scope and intensity during the period concurrent with the “chain murders” in Iran, from 1988-1998. The increasing reliance on assassinations was largely the handiwork of President Rafsanjani’s intelligence minister Ali Fallahian, who was also the chief architect of the domestic assassination campaign against regime opponents. After the MOI was purged of many of its most hardline staffers in the wake of the discovery of the chain murders, the international assassinations tapered off as well.
One of the more sensational assassinations during this period took place in Switzerland in April 1990 and targeted Kazem Rajavi, the brother of MEK leader Massoud Rajavi. Two cars ran Rajavi’s vehicle off the road, after which armed gunmen exited one of the cars and executed Rajavi. Swiss investigators issued a report naming 13 suspects believed to be Iranian intelligence officers. According to the report, “all 13 came to Switzerland on brand-new government service passports, many issued in Tehran on the same date. Most listed the same personal address, Karim-Khan 40, which turns out to be an intelligence ministry building.”
In August 1991, Iranian operatives stabbed to death one of the most prominent exiled opposition figures, Dr. Shapour Bakhtiar, and his secretary in his Paris apartment. Bakhtiar was a political opponent of the Shah who the Shah appointed as his final prime minister in a last-ditch effort to prop up his crumbling government at the end of 1978. During his short-lived tenure, Bakhtiar sought to rapidly implement political reforms in an effort to pacify Khomeini’s revolutionary forces. Khomeini, insisting on nothing less than the overthrow of the monarchy, rejected Bakhtiar’s government and denounced him for collaborating with the Shah. Bakhtiar fled Iran shortly after the Islamic Revolution in April 1979.
Bakhtiar was one of the former regime figures marked for assassination by Ayatollah Khalkhali, the first magistrate of Iran’s revolutionary courts immediately following the revolution. Upon his emergence in Paris, Bakhtiar founded and led the National Movement of the Iranian Resistance. This organization connected Bakhtiar to Ali Akbar Tabatabai, who served as Bakhtiar’s primary spokesman in the U.S. In July 1980, Khomeini thwarted a coup plot led by Iranian military officers at the Nojeh air base which Bakhtiar was accused of backing. Shortly thereafter, Bakhtiar survived the first assassination attempt on his life by Khomeini’s agents. One of the would-be assassins later implicated the Iranian regime in the plot, stating in a 1991 interview, “I had no personal feelings against Bakhtiar … It was purely political. He had been sentenced to death by the Iranian Revolutionary Tribunal. They sent five of us to execute him.” In 1991, three Iranian operatives were dispatched for another assassination attempt on Bakhtiar, this one successful. Two of the assassins escaped to Iran while the third was apprehended in Switzerland and extradited to France. The assassin received a life sentence, but was paroled in 2010 and subsequently repatriated to Iran.
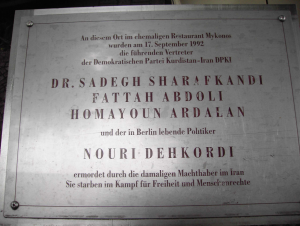 A plaque commemorating the victims of the 1992 Mykonos Restaurant assassination plot in Berlin.
A plaque commemorating the victims of the 1992 Mykonos Restaurant assassination plot in Berlin.
Perhaps the most “daring and public“ incident during this time period was the elaborately planned assassination of four Kurdish democracy activists at the Mykonos Restaurant in Berlin, Germany on September 17, 1992. The Mykonos plot was carried out by a Hezbollah cell acting under the orders of the Iranian government and with direct participation by MOI operatives. An Iranian defector with ties to the security establishment alleged that the decision to carry out the attack was made by Iran’s Special Affairs Committee, which included President Rafsanjani, Intelligence Minister Fallahian, former Foreign Minister Ali Akbar Velayati, and Supreme Leader Khamenei himself. In the run up to the attack, Fallahian gave a series of interviews in which he boasted that Iran surveilled dissidents abroad and had already eliminated some top regime opponents.
An MOI operative trained in Lebanon led the “attack group” behind the Mykonos assassination and served as one of the two gunmen. The other gunman, and many of the co-conspirators in the attack were Hezbollah members based in Germany. The MOI was instrumental in the logistics of the attack, conducting surveillance of the targets and securing the weapons and silencers used. Following Germany’s investigation, into the attack, the federal prosecutor issued an arrest warrant for Ali Fallahian for ordering the attack. Khamenei, Rafsanjani, and Velayati would also be implicated for their roles in ordering and approving the plot by the German judge presiding over the trial of five of the participants in the attack.
The revelation of the MOI’s role in the chain murders, along with rising international condemnation and pressure from countries where Iranian intelligence operatives had carried out assassinations, led the Islamic Republic to abandon the practice by 1999. Since that time, Iran’s external intelligence apparatus has shifted its focus to harassment, intimidation, and delegitimization of dissidents abroad.
Embedded Iranian intelligence agents “have been known to monitor dissidents by infiltrating and observing their meetings and speeches, and MOI officers often want dissidents to know they are being watched so that they will be intimidated.” Iranian intelligence frequently engages in disinformation campaigns to tarnish the reputation of dissident groups abroad and to sour their relations with host countries, a tactic it learned from the Soviet KGB. In 2013, for instance, at the Obama administration’s urging, Albania offered asylum to up to 2000 Iranian MEK dissidents. In response to their presence, Iranian media outlets began publishing articles in Albanian meant to discredit the MEK. In May 2017, the Islamic Republic of Iran Broadcasting (IRIB) announced the launch of a 24-hour Balkan Network featuring Bosnian and Albanian language programming meant both to propagate the Iranian regime’s religious and geopolitical worldview, and to influence public opinion against the MEK.
Iran has also launched complex operations in recent years to lure dissidents into third countries, which offer Iranian intelligence a permissive environment, and to kidnap them while there. Recent cases include the late dissident journalist Ruhollah Zam, the son of a former regime official, who ran a popular Telegram channel called Amad News. Beginning in 2011, Zam had lived in exile in France under police protection. In 2019, he was lured to Iraq with false promises of funding for a media project, and abducted there by the IRGC. Zam was later executed in December 2020 for the crime of “corruption on earth.”
The regime also kidnapped Jamshid Sharmahd, a California-based operative of the Kingdom Assembly of Iran’s Tondar opposition group, in Dubai. After, based on cell phone data, Iranian operatives took him to Oman and then to Iran. The regime accused Sharmahd, a German citizen, of complicity in a 2008 attack on a mosque, but Sharmahd’s family denies the allegation, saying he was merely a spokesman for the group. A similar modus operandi was employed in Iran’s abduction of Habib Chaab in Turkey. Chaab, a founder of the Arab Struggle Movement for the Liberation of Ahvaz (ASMLA) and a Swedish citizen, was lured to Istanbul using an MOI “honey trap.” This entailed the use of a female Iranian spy who enticed Chaab to travel to Turkey under the pretext of a romantic meeting. He was then kidnapped and smuggled across the border into Iran. There, he appeared on state television, with an alleged coerced confession to engaging in terrorism. Thus, the IRGC and MOI have both been using this tactic.
In July 2021, the U.S. Department of Justice unsealed an indictment charging an Iranian intelligence officer, three Iranian intelligence “assets,” and a co-conspirator based in California with plotting to kidnap Masih Alinejad, a dissident Iranian journalist and human rights activist residing in Brooklyn who was a vocal critic of the regime’s mandatory veiling policies. According to Alinejad, Iran’s MOI orchestrated the plot, using laundered money to pay private investigators to surveil Alinejad in her Brooklyn home with the eventual objective of kidnapping and forcibly repatriating her to Iran. The Iranian intelligence agents reportedly sought to pressure her family members residing in Iran to lure her to a third country where they would capture her, and researched using military speedboats to initially extricate her to Venezuela. An Iranian writer, Roya Hakakian, revealed in 2021 that the FBI had warned her that Iranian operatives were targeting her as well.
Exporting the Revolution
Iran made the decision to spread its revolutionary ideology through terrorism and subversion in the early years following the Islamic Revolution. At a 1982 conference in Tehran, former IRGC commander Javad Mansouri proclaimed, “Our revolution can only be exported with grenades and explosives.” In the same speech, Mansouri called upon Iran to transform every Iranian embassy into an intelligence center and a base to export the revolution.
The regime adopted Mansouri’s strategy, and as a result, Iran seeks to embed undercover intelligence agents and IRGC operatives in its foreign embassies, which are often heavily scrutinized by host countries. According to Stratfor, “Iran includes large intelligence sections in its embassies and missions, and official cover often includes positions in the Foreign Ministry abroad. … The MOI also employs non-official cover for its officers, including those of student, professor, journalist and employee of state-owned or state-connected companies (e.g., IranAir and Iranian banks).”
In communities where Iran has an embassy or consulate, it typically also operates an interconnected web of mosques, cultural centers, educational institutions, charities, and media organs. Many of these organizations double as fronts for the MOI and IRGC-IO to embed agents. Within these institutions, Iranian intel operatives fulfill a number of foreign policy objectives on behalf of the Iranian regime.
Among their primary duties, Iranian agents seek out and establish ties to potential recruits from local communities sympathetic to Iran’s Islamic Revolution for training and indoctrination oriented toward radicalization. Recruitment often occurs at business conferences and religious or cultural events. These recruits in turn provide the Iranian regime a support base in host countries, and Iran’s intelligence services pay for the most ideologically committed individuals to travel to Iran for specialized religious and paramilitary training. Iran’s recruits can then use the cover of the Iranian-funded and directed religious, cultural, and educational institutions to establish networks and exchange lessons learned. Iran is able to plug some recruits into existing Hezbollah networks, where they assist the global terrorist organization in its criminal and violent exploits.
Another function of embedded Iranian intelligence agents is to provide logistical and operational support for Hezbollah terrorist attacks in conjunction with the IRGC-Quds Force. The 1992 and 1994 bombings in Buenos Aires of the Israeli embassy and AMIA Jewish Community Center provide a case study for the modus operandi of Iran’s intelligence services in facilitating terrorist attacks.
In the mid-1980s, Iran dispatched a committed revolutionary, Mohsen Rabbani, to Latin America to build out “an intelligence system that would report to the Iranian Embassy in Buenos Aires and then up to Tehran.” Serving as the imam of a major Iranian-directed mosque, Rabbani propagandized on behalf of Iran’s revolutionary government, cultivating and training disciples willing to conduct espionage and subversive activities to further Iranian objectives. The intelligence network formed by Rabbani and his disciples provided logistical and operational support to the embedded Hezbollah network that carried out the 1992 and 1994 bombings targeting Buenos Aires’s Jewish/Israeli community. Rabbani’s team surveilled locations, provided documentation and communications support to the bombers, and in the case of the AMIA attack, handled all details pertaining to the purchase, hiding, and arming of the van to be used in the bombing.
A subsequent investigation of the bombings by Argentinean prosecutor Alberto Nisman fingered Rabbani, who had built a network of “local clandestine intelligence stations designed to sponsor, foster and execute terrorist attacks,” as the mastermind behind the attacks. Immediately preceding the AMIA bombing, Iran moved to suddenly designate Rabbani as the Cultural Attaché to the Iranian Embassy in Buenos Aires, accordingly granting him a diplomatic passport. This hasty appointment enabled Rabbani to use the cover of the Iranian embassy “to go about providing material support for the operation with relative ease, while at the same time guaranteeing him diplomatic immunity following the attack.”
Nisman’s report further concluded that “the decision to carry out the AMIA attack was made, and the attack was orchestrated, by the highest officials of the Islamic Republic of Iran at the time, and that these officials instructed Lebanese Hezbollah—a group that has historically been subordinated to the economic and political interests of the Tehran regime—to carry out the attack.” An FBI investigation into the attack found that Rabbani used his perch in the office of the Cultural Attaché to stay in frequent contact, under the radar, with the Hezbollah operatives carrying out the attack.
The Iranian officials behind the attacks were the Special Affairs Committee, the same officials who had orchestrated the Iranian campaign of dissident assassinations abroad in venues like Mykonos. Nisman’s findings precipitated the issuance by an Argentinean court of international arrest warrants for nine high-ranking Iranian and Hezbollah officials, including former Iranian President Ali Akbar Hashemi Rafsanjani, former Iranian Intelligence Minister Ali Fallahian, former Foreign Minister Ali Akbar Velayati, and Mohsen Rabbani.
Since the bombings in Argentina, Iran has sought to embed operatives and intelligence contacts throughout Latin America, Europe, and Africa. These agents have helped Iran spread its revolutionary ideology around the world and facilitated terror attacks at the regime’s behest. Between 2011 and 2013, the IRGC-QF and Hezbollah attempted more than 30 attacks on foreign soil, often with assistance from the MOI. Among the targets were American, Saudi, and Israeli interests in the U.S., Thailand, India, Nigeria, Kenya, Bulgaria, and Cyprus. Iranian intelligence operatives or foreign recruits under their command were involved in the scouting of targets and material provision of funds and weaponry/explosives to facilitate the attacks, many of which were thwarted by local authorities.
In October 2011, U.S. agents disrupted an assassination plot allegedly directed by the Iranian government targeting Saudi Arabia’s then-ambassador to Washington, Adel al-Jubeir. The FBI’s investigation into the plot (code named Operation Red Coalition) discovered that Mansoor Arbabsiar, a dual U.S.-Iranian citizen, and Gholam Shakuri, an IRGC-QF commander, were planning to kill al-Jubeir with a bomb at a restaurant. They also planned to subsequently bomb both the Saudi and Israeli embassies in Washington D.C. and were also considering carrying out attacks in Buenos Aires. Arbabsiar was arrested on September 29, 2011 at JFK International Airport, confessing to the plot and receiving a 25-year prison sentence, while Shakuri remains uncaptured.
Similar plots continue to this day. Iran is increasingly engaged in espionage activities on German individuals, for instance. In March 2017, it was reported that the Quds Force intelligence agents in Germany hired a Pakistani student known as Syed Mustafa H. to gather information on pro-Israeli individuals and institutions. The student was asked to surveil former MP Reinhold Robbe, who previously headed the German-Israeli parliamentary group and served as President of the German-Israeli Society. Security authorities suspect that information was gathered for potential retaliatory measures against Israel-friendly individuals in case Israel launched air strikes on Iranian nuclear facilities. Following this incident, police conducted a series of raids linked to 10 other Iranian spy suspects, but no arrests were made.
In early July, 2018, authorities in France, Belgium, and Germany thwarted a planned Iranian terror attack targeting the Paris convention of the National Council of Resistance in Iran, the political wing of the MEK. Two Iranian suspects were intercepted in Belgium carrying 500 grams of explosives to the convention. An Iranian diplomat, Assadollah Assadi—believed to be the MOI station chief in Vienna—was arrested in Germany on suspicion of having contacts with the would-be bombers. The foiled plot bore many of the hallmarks of previous Iran-backed terror plots, including an intelligence official using the diplomatic cover of an Iranian embassy to coordinate the attack. In February 2021, Assadi and his co-conspirators were convicted in a Belgian court for their roles in the plot and given sentences ranging from 15-20 years. The convicted terrorist returned to Iran in late May 2023 in exchange for Iran’s release of various European prisoners, who had been taken hostage on trumped-up charges.
In August 2018, U.S. federal authorities arrested two individuals, Ahmadreza Mohammadi Doostdar and Majid Ghorbani, for acting as agents of the Government of Iran, violating U.S. sanctions, and conspiracy. According to the arrest affidavit, Doostdar, a dual U.S.-Iranian national, and Ghorbani, an Iranian national with permanent U.S. residency, acted on behalf of the Iranian government “in order to conduct covert surveillance on and to collect information from and about the Mohahedin-e Khalq (MEK) and Israeli/Jewish groups, and to provide this information back to the Government of Iran for the purpose of enabling the Government of Iran to target these groups.” The affidavit detailed the intelligence tradecraft methods employed by the alleged Iranian agents to conceal their activities and detect countersurveillance. Prosecutors allege that Doostdar paid Ghorbani $2000 for photographs he took at pro-MEK demonstrations in 2017.
In October 2018, Denmark’s intelligence service Politiets Efterretningstjeneste (PET) accused an “Iranian intelligence agency” of plotting to assassinate an exiled leader of an Iranian-Arab separatist group on Danish soil in the previous month. The plot was apparently intended as retaliation for a September 22 attack on an Iranian military parade in southwest Iran. The target, however, has denied his group’s involvement in that attack and a different Arab separatist movement has claimed credit. According to Danish and Swedish police, a Norwegian man of Iranian descent was seen in late September taking photographs of the Arab dissident’s residence with the intent of passing on “the information to an Iranian intelligence service with a view to the information forming part of the plans to assassinate the leader.” The Iranian agent was arrested in Sweden on October 21.
In November 2019, an Iranian dissident, Masoud Molavi Vardanjani, was shot dead in Istanbul, Turkey. According to Turkish authorities, Vardanjani had previously worked in cyber security for the Iranian Defense Ministry, but while living in Turkey had launched a campaign to expose financial and moral corruption of senior regime officials. In March 2020, Turkish officials alleged—based on the testimonies of the suspected gunman and other Turks and Iranians detained in connection to the plot—that the killing was carried out at the direction of two Iranian intelligence officers with diplomatic passports at the Iranian consulate in Istanbul. A senior U.S. official concurred with Turkey’s findings, telling Reuters, “Given Iran’s history of targeted assassinations of Iranian dissidents and the methods used in Turkey, the United States government believes that Iran’s Ministry of Intelligence and Security (MOIS) was directly involved in Vardanjani’s killing.”
In March 2020, Afghanistan reportedly expelled two Iranian diplomats for their suspected involvement in intelligence activities on behalf of the Iranian government. One of the diplomats served as the cultural attaché at the Iranian embassy in Kabul and the other was allegedly an influential member of the IRGC Quds Force.
In June 2020, a former Iranian judge, Gholamreza Mansouri, who was awaiting extradition back to Iran, was found dead at a hotel in Romania. Mansouri, who was notorious for the jailing of journalists, had been implicated in a corruption case in Iran. While investigations are ongoing, indications of foul play have emerged in Tehran. Former Secretary of Iran’s Expediency Council Mohsen Rezaei dubbed his death a “murder” and the editor-in-chief of Mashregh News, which is close to the IRGC, proclaimed “As of today, Romania is a point of strategic depth [for Iran].” A day later, there was an attempted assassination on a Kurdish Iranian dissident, Sadegh Zarza, in the Netherlands. The Dutch government in the past has accused Iran of hiring criminal gangs to target dissidents inside the country.
In August 2020, the domestic intelligence service for the German state of Saarland alleged that Iran had undertaken illicit procurement efforts for weapons of mass destruction and their delivery systems, presumably referring to ballistic missiles, in Germany during the previous year. The agency’s report detailed how countries like Iran embed intelligence staff within Germany through official (embassies and consulates) and semi-official (news agencies, airline offices) channels. According to the report, “The intelligence staff there, supposedly working as diplomats or journalists, conduct open or covert information gathering themselves or provide support in intelligence operations that are carried out directly by the headquarters of the intelligence services in their home countries. … The focus of their respective procurement activities is based on current political requirements or economic priorities.”
The Saarland report followed a June 2020 report from the domestic intelligence agency for the German state of Baden-Württemberg that also alleged Iran was undertaking illicit weapon of mass destruction procurement activities in Germany. The report from the heavily industrialized state noted that German companies should be wary of Iranian front companies seeking to circumvent export controls by obtaining dual use materials and bringing them to bypass countries, such as the United Arab Emirates, Turkey, and China, with the ultimate destination being Iran.
In September 2020, U.S. intelligence reports alleged that Iran is plotting to assassinate the American ambassador to South Africa in retaliation for the January U.S. drone strike that killed IRGC Quds Force commander Qassem Soleimani in Iraq. According to a U.S. government official, Iran’s embassy in Pretoria is involved in the plot which first came to light in the spring. More recently, intelligence about the threat to the ambassador has reportedly become more specific.
Iran has reportedly cultivated an extensive network of spies in South Africa in recent years, embedding agents through Iran’s diplomatic channels in the country as well as covers including Iran Air, the Islamic Republic of Iran Broadcasting and the Islamic Republic of Iran Shipping Lines. Iran’s intelligence activities in the country have included seeking workarounds for international sanctions targeting Tehran, illicit procurement attempts to acquire proscribed missile components through the use of front companies, and establishing confirmed links to terrorist and extremist organizations. According to an assessment by South Africa’s State Security Agency, Iran’s general modus operandi is to use the cover of diplomacy to send and store arms in Iranian embassies and diplomatic missions, recruit among local populations to establish Hezbollah or terrorist cells, and then train these cells to carry out terrorist plots or assassinations, giving Iran a degree of plausible deniability as to its involvement.
In November 2020, Israel was behind the assassination of Iran’s leading nuclear scientist, Mohsen Fakhrizadeh, according to a U.S. official. The operation represented a monumental intelligence failure for Iran, and has led to the MOI and IRGC-IO casting blame on each other for the lapse. In the time since, Iran’s intelligence services have sought to retaliate through a number of plots targeting Israeli tourists, diplomats, and businessmen abroad.
In January 2021, Indian authorities alleged that the IRGC-Quds Force helped a local Shi’a terror cell carry out a bombing outside the Israeli embassy in New Delhi. The cell, calling itself “Indian Hezbollah,” left a handwritten note near the scene vowing to avenge the killings of Qassem Soleimani and Mohsen Fakhrizadeh.
In September 2021, Cypriot authorities thwarted a plot, which Israel alleges was orchestrated by Iran, involving an Azerbaijani hitman. The hitman had repeatedly staked out an office complex where many Israelis worked, and was captured with a gun and silencer on him immediately before he was about to carry out his killings.
There has also been an uptick in Iran threat reporting in Colombia. In November 2021, Colombian media reported that Israel had evacuated a former intelligence official and diplomat who had recently opened a surveillance technology company in Bogota from the country because he was being surveilled by Hezbollah operatives. According to the Mossad, Hezbollah was seeking to assassinate the former Israeli intelligence official, as well as U.S. diplomats stationed in Bogota. Colombia’s defense minister additionally revealed that Colombia expelled two Hezbollah operatives two months prior who were planning a “criminal act” in the country. The increased Hezbollah activity in Colombia has raised concerns about the group using neighboring Venezuela as a haven to plot terrorist attacks and establish connections to other terrorist and criminal networks. There were additional reports in June 2021 that Colombia’s intelligence agency issued a security alert that two Israeli businessmen were targets of an assassination attempt by a senior Quds Force operative Rahmat Asadi. It remains unclear if there was overlap between the Hezbollah and the Quds Force plots.
Also, in November 2021, an Israeli television network reported that local intelligence authorities in unspecified African countries arrested five individuals who were reportedly planning to attack Israeli targets in Africa. The five suspects reportedly were recruited by the IRGC-Quds Force and given training and unspecified materials in Lebanon before being dispatched to Africa, where they were instructed to pose as religious students and find Israeli interests to attack. The suspects reportedly had traveled to Ghana, Senegal, and Tanzania before their capture. This followed reports earlier in 2021 of Ethiopian authorities thwarting an Iranian intelligence cell that was plotting attacks on Emirati diplomatic facilities in Addis Ababa and Sudan. Likewise, in February 2022, Turkish authorities implicated Iran in a plot to assassinate Yair Geller, an Israeli and Turkish citizen, and businessman, in retaliation for killing Iran’s former Deputy Defense Minister Mohsen Fakhrizadeh.
Separately, Iran continues to eye assassination operations on the U.S. homeland to avenge the death of Soleimani. In March 2022, U.S. media reports suggested that former U.S. Secretary of State Mike Pompeo, former U.S. National Security Advisor John Bolton, and former U.S. Special Representative for Iran Brian Hook have all received federal protection because of “serious and credible threats” to their lives from Iran. According to CBS News, Pompeo’s security detail “rivals one that is typical for a current cabinet member” and that on at least three occasions, a specific threat required security for Hook, most recently in November 2021. Such threat assessments are consistent with the U.S. intelligence community's finding from the Worldwide Threat Assessment of 2022 that Iran remains interested in developing networks inside the United States—an objective that it has pursued for more than a decade.
On August 10, 2022, the U.S. Department of Justice charged an Iranian national and member of the Islamic Revolutionary Guard Corps (IRGC) for plotting to assassinate former U.S. National Security Advisor John Bolton on behalf of the IRGC’s Quds Force. More specifically, he was charged “with use of interstate commerce facilities in the commission of murder-for-hire, and with providing and attempting to provide material support to a transnational murder plot.” Shahram Poursafi, currently at large abroad, attempted to pay individuals in the U.S. $300,000 via a cryptocurrency to murder John Bolton, likely in retaliation for the January 2020 death of Qassem Soleimani, the U.S. Justice Department said. Poursafi allegedly told his recruit that the order to carry out the assassination was sent down through a chain of command, suggesting that he was not a rogue operative within the Quds Force. Poursafi assigned his source with a separate assassination job in March, but the Justice Department has not revealed the target of the second plot. If captured and convicted on both counts, Poursafi faces up to 25 years in prison, and $500,000 in fines.
On June 1, 2023, the U.S. Department of the Treasury announced the designation of several individuals under counterterrorism authority E.O 13224. Mohammad Reza Ansari, an IRGC Quds Force operative, was designated for his involvement in a plot to assassinate two former U.S. government officials, alongside the previously mentioned Poursafi. Additionally, Hossein Hafez Amini, an IRGC affiliate in Turkey, was designated for providing material assistance to Quds Force operations in Turkey through his connections in the airline industry. Furthermore, two senior officials within the IRGC Intelligence Organization were also designated. Rouhallah Bazghandi, the IRGC-IO Counterespionage Department Chief, was designated for his role in planning and overseeing operations in Iraq and Syria, as well as targeting Israeli nationals. Reza Seraj, the IRGC-IO Foreign Intelligence Chief, was designated for his involvement in failed intelligence operations in Asia, along with targeting U.S. and Israeli nationals.
Iran has also stepped up its targeting of Israelis in the aftermath of a string of mysterious deaths inside Iran in May and June 2022, including the deputy commander of the Quds Force’s Unit 840 Hassan Sayyad Khodaei. Khodaei reportedly was responsible for terrorist plots against Israelis in New Delhi and Thailand in 2012, and more recent incidents directed at Israeli diplomats in Turkey, an American general in Germany, and a French intellectual. As Iran has experienced multiple attacks at home, Turkey has emerged as a central launchpad for its attempted attacks and kidnappings of Israelis to restore deterrence. Iran has not only been aiming to strike at diplomats and businessmen in Turkey, but also at tourists. In June 2022, Israel’s Foreign Ministry took the unusual step of asking Israelis to cancel flights to Turkey and return home immediately due to an imminent threat. As Israel’s foreign minister warned, “these terrorists are aimed at vacationing Israelis. They are selecting, in a random but deliberate manner, Israeli citizens with a view to kidnapping or murdering them.”
The Cyber Threat
In 2010, over 15 Iranian nuclear facilities were targeted by the Stuxnet computer virus, a worm jointly developed by the U.S. and Israel that destroyed nearly 1000 centrifuges. The attack exposed the weakness of Iran’s cyber defenses, leading Iran to rapidly seek the advancement of offensive and defensive cyber capabilities. By 2011, Iran created a “cyber command” to combat threats and conduct retaliatory operations. Since that time, Iran has “become increasingly adept at conducting cyber espionage and disruptive attacks against opponents at home and abroad,” according to a Carnegie Endowment report on the Iranian cyber threat. The 2018 Worldwide Threat Assessment of the U.S. Intelligence Community concluded that Iran “will continue working to penetrate U.S. and Allied networks for espionage and to position itself for potential future cyber attacks.”
Iran has carried out cyber attacks against the U.S. on several occasions. In May 2016, the U.S. Department of Justice announced indictments against seven Iranian cyber specialists linked to the Iranian government and Islamic Revolutionary Guard Corps (IRGC) for cyber attacks against U.S. banks and a New York dam. The men were accused of carrying out distributed denial of service attacks in which they hacked into bank servers and clogged it with data, preventing legitimate traffic, against 46 U.S. financial institutions, and attempting to hack into the control system of a New York dam between 2011 and 2013. In 2014, Iranian “hacktivists” carried out a data deletion attack against the network of a Las Vegas casino owned by Sheldon Adelson, an outspoken opponent of Iran’s nuclear program. The scope and sophistication of the attack indicated knowledge by the Iranian government, given the regime’s strict controls over internet usage. In March 2018, federal prosecutors unsealed indictments against nine Iranians accused of carrying out cyber attacks on behalf of the IRGC who stole data for financial gain from “144 American universities, 36 American companies and five American government agencies.”
In August 2018, Facebook and Twitter purged hundreds of Iran-based groups and accounts that appeared to be part of a coordinated, inauthentic effort linked to Iranian state media to spread political content on four different continents, including in the U.S. The unusual activity was detected by a private cybersecurity firm called FireEye, which alerted the social media companies. In a statement, FireEye said, “This operation is leveraging a network of inauthentic news sites and clusters of associated accounts across multiple social media platforms to promote political narratives in line with Iranian interests.” The inauthentic pages sought to back Iranian foreign policy imperatives, and featured content that was pro-Iranian and pro-Palestinian, or anti-American, anti-Israeli, and anti-Saudi. Many pages reportedly promoted Quds Day, the Iranian regime-sponsored global day of protest against Israel.
In 2019, Iran engaged in a campaign of stepped-up malign activities around the region as the Trump administration’s “maximum pressure” campaign increasingly took effect, harming Iran’s economy. As part of its campaign, Iran also stepped up its malign cyber activities. In June 2019, the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) warned, “CISA is aware of a recent rise in malicious cyber activity directed at United States industries and government agencies by Iranian regime actors and proxies. … Iranian regime actors and proxies are increasingly using destructive ‘wiper’ attacks, looking to do much more than just steal data and money. These efforts are often enabled through common tactics like spear phishing, password spraying, and credential stuffing.”
In July 2019, U.S. Cyber Command tweeted that they discovered active misuse of a bug in Microsoft Outlook. FireEye traced the activity to a threat group called APT33, which is allegedly working at the behest of the Iranian government as part of a coordinated campaign against “U.S. federal government agencies and financial, retail, media, and education sectors.” Following the January 2020 drone strike that killed IRGC Quds Force commander Qassem Soleimani, Iran-based attempts to hack U.S. federal, state and local government websites jumped 50% and nearly tripled worldwide.
Iran has turned its cyber capabilities against U.S. allies as well. In 2012 and then again in late 2016 and early 2017, Iranian-origin malware called Shamoon targeted the Saudi Arabian government and private sector. The 2012 attack damaged or destroyed nearly 30,000 computers belonging to the Saudi state oil company, Aramco, and the latest attacks deleted data on dozens of public and private computer networks. In July 2018, Germany’s domestic intelligence service found that Iranian cyber attacks targeting “the German government, dissidents, human rights organizations, research centers and the aerospace, defense and petrochemical industries” have been growing since 2014. The efficacy of the Iranian cyber attacks on Germany led the report’s authors to conclude that the operations are initiated and guided by intelligence agencies.
In March 2020, Reuters revealed hackers linked to Iran’s government had attempted to infiltrate the personal email accounts of staff members of the World Health Organization during the coronavirus pandemic. The same report indicated that such operations in the past have been characterized by experts as intelligence-gathering exercises.
In July 2021, cyber-security firm Proofpoint reported that the IRGC-linked hacking collective, Charming Kitten, had conducted a sophisticated spear phishing campaign that involved spoofing the website and impersonating staff of a British university in order to trick U.S. and U.K. based Middle East scholars and experts into registering for fake academic conferences, collecting personal information, including e-mail addresses and passwords, in the process. Google also warned of such cyberattacks by Charming Kitten in a threat alert issued in October 2021. UANI itself has been targeted as a part of this activity. In November 2021, the FBI warned that Iranian hackers had visited cybercriminal websites for sensitive data stolen from American and foreign organizations for future operations.
In 2022, the director of the FBI revealed that in June 2021, during the negotiations to revive the nuclear deal, Iran attempted to launch a cyberattack on Boston Children’s Hospital. He called it the most “despicable” attacks he had ever seen.
While Iran’s cyber capabilities do not rival those of the U.S., China, Russia, or even Israel, the asymmetric nature of the cyber domain has enabled Iran to carry out some of “the most sophisticated, costly, and consequential attacks in the history of the internet.” Cyberwarfare enables Iran to mask the source of attacks, but U.S. indictments against Iranians engaged in cyber sabotage and espionage revealed operations that “required costly infrastructure, including dedicated servers and dozens of domain names, in addition to personnel time,” indicating the involvement of Iran’s intelligence services.
Receive Iran News in Your Inbox.
Eye on Iran is a news summary from United Against Nuclear Iran (UANI), a section 501(c)(3) organization. Eye on Iran is available to subscribers on a daily basis or weekly basis.
Receive Iran News in Your Inbox
The Iran nuclear deal is done. And the world's biggest companies have already visited Tehran ready to strike a deal when sanctions end. These businesses will add even more to Iran's bottom line. And that means continued development of nuclear technologies and more cash for Hamas and Hezbollah.